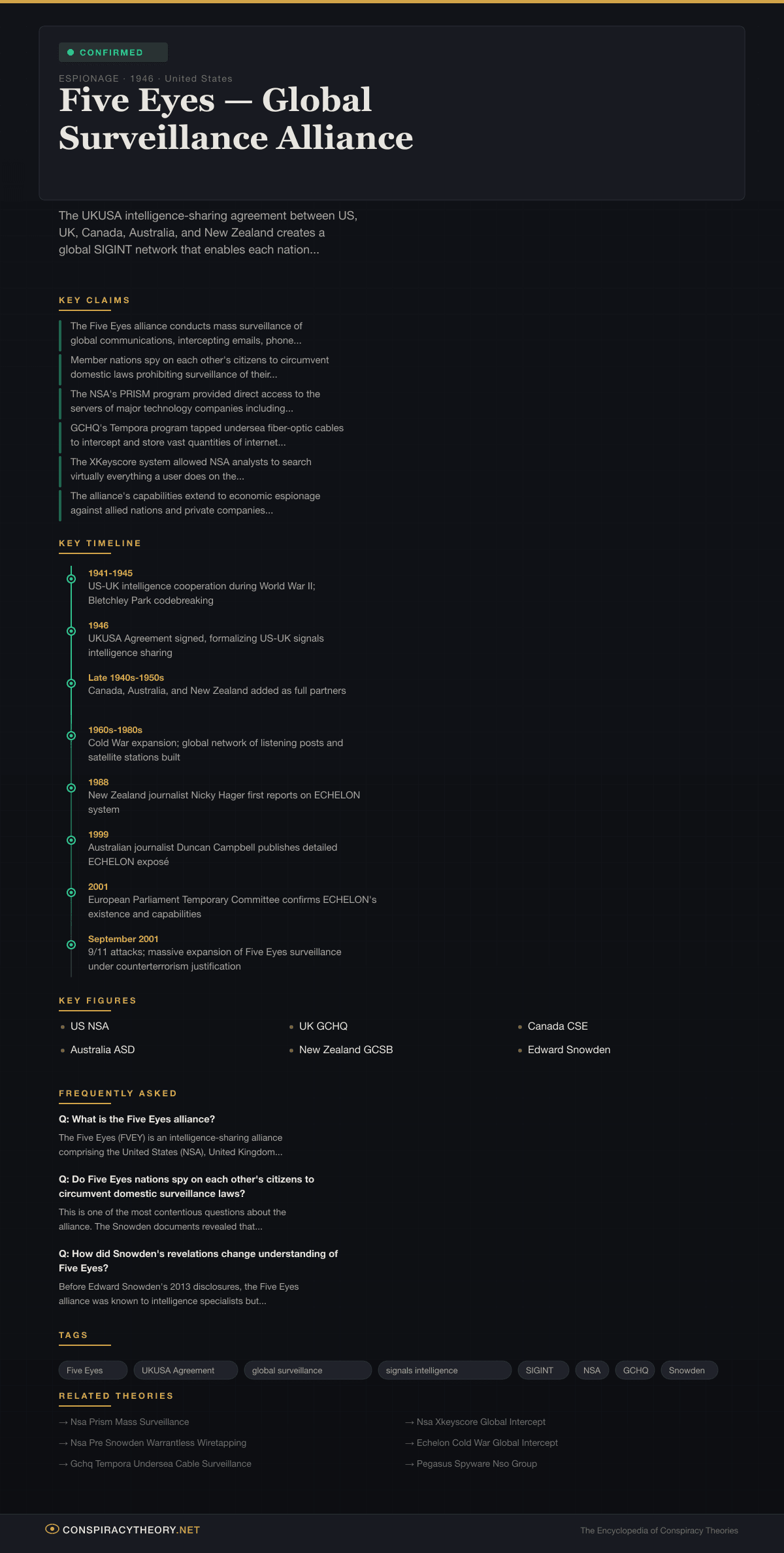
Five Eyes — Global Surveillance Alliance
Overview
The Five Eyes alliance is a confirmed intelligence-sharing network among the United States, the United Kingdom, Canada, Australia, and New Zealand that constitutes the most extensive signals intelligence cooperation arrangement in the world. What was once characterized as a conspiracy theory — that these five English-speaking nations had formed a secret alliance to conduct global surveillance, sharing intercepted communications to circumvent each other’s domestic privacy laws — was proved substantially correct by the 2013 Snowden revelations.
The alliance, rooted in the 1946 UKUSA Agreement, divides the world into collection areas among its members, with each nation responsible for intercepting communications within its geographic sphere and sharing the intelligence with all partners. The result is a global surveillance network of extraordinary scope, capable of intercepting telephone calls, emails, internet activity, and satellite communications across virtually every country on Earth.
While intelligence officials defend the alliance as essential to national security and counterterrorism, the Snowden documents revealed that Five Eyes surveillance extended far beyond targeted intelligence collection against specific threats. Programs like PRISM, XKeyscore, and Tempora enabled the bulk collection of communications data from billions of ordinary people worldwide, with minimal oversight and largely without public knowledge. The confirmation of these capabilities transformed the Five Eyes from a niche intelligence concern into one of the most significant privacy issues of the 21st century.
Origins & History
The Five Eyes alliance traces its origins to the intelligence cooperation between the United States and the United Kingdom during World War II. American and British codebreakers worked closely together on cracking Axis communications, most famously at Bletchley Park where the Enigma machine was broken. This wartime partnership produced extraordinary intelligence dividends and established deep institutional relationships between the two nations’ signals intelligence agencies.
In 1946, these wartime arrangements were formalized in the UKUSA Agreement (also known as the BRUSA Agreement), a secret treaty between the US and UK for sharing communications intelligence. The agreement divided the world into spheres of collection responsibility and established protocols for sharing intercepted signals intelligence (SIGINT). The text of the agreement was classified for decades — its existence was not officially acknowledged until 2010, when the full text was declassified by the UK and US governments.
Canada, Australia, and New Zealand were incorporated into the arrangement as “second parties” in the late 1940s and early 1950s, reflecting their roles in the British Commonwealth and their geographic positioning, which provided coverage of areas that the US and UK alone could not easily monitor. Canada’s Communications Security Establishment (CSE), Australia’s equivalent (now the Australian Signals Directorate, ASD), and New Zealand’s Government Communications Security Bureau (GCSB) became full partners in the intelligence-sharing network.
During the Cold War, the Five Eyes alliance was primarily oriented toward monitoring Soviet and Warsaw Pact communications. Each member nation operated listening posts, satellite ground stations, and other collection facilities within its sphere of responsibility. The ECHELON system, exposed through investigative journalism in the 1990s, revealed that the alliance had developed a global network of satellite interception stations capable of intercepting phone calls, faxes, and data communications worldwide. A 2001 European Parliament report confirmed ECHELON’s existence and capabilities, concluding that the system was used not only for military and diplomatic intelligence but also for economic espionage.
The alliance’s capabilities expanded dramatically after the September 11, 2001 attacks. Under the justification of counterterrorism, the NSA and its Five Eyes partners massively expanded their collection programs. New authorities and technologies enabled the bulk collection of telephone metadata, internet communications, and financial transactions on a scale that would only be revealed a decade later.
The watershed moment came in June 2013, when Edward Snowden, a contractor working for the NSA, began disclosing classified documents to journalists Glenn Greenwald, Laura Poitras, and Barton Gellman. The documents revealed the specific programs, capabilities, and scale of Five Eyes surveillance with unprecedented detail, transforming public understanding of the alliance and triggering a global debate about privacy, security, and government overreach.
Key Claims
- The Five Eyes alliance conducts mass surveillance of global communications, intercepting emails, phone calls, text messages, and internet activity from billions of people (confirmed)
- Member nations spy on each other’s citizens to circumvent domestic laws prohibiting surveillance of their own populations (substantially confirmed)
- The NSA’s PRISM program provided direct access to the servers of major technology companies including Google, Apple, Microsoft, Facebook, and Yahoo (confirmed with nuances)
- GCHQ’s Tempora program tapped undersea fiber-optic cables to intercept and store vast quantities of internet traffic (confirmed)
- The XKeyscore system allowed NSA analysts to search virtually everything a user does on the internet (confirmed)
- The alliance’s capabilities extend to economic espionage against allied nations and private companies (partially confirmed)
- Five Eyes surveillance is conducted with minimal meaningful oversight and largely without public knowledge (substantially confirmed for the pre-Snowden era)
- The alliance represents a permanent, extra-democratic surveillance infrastructure that operates beyond the reach of normal democratic accountability (argued and debated)
Evidence
The evidence for Five Eyes surveillance capabilities is overwhelming, primarily sourced from the Snowden archive of classified documents.
PRISM: Documents revealed that the NSA’s PRISM program collected internet communications from at least nine major US technology companies: Microsoft, Yahoo, Google, Facebook, PalTalk, AOL, Skype, YouTube, and Apple. The program operated under Section 702 of the Foreign Intelligence Surveillance Act and was authorized by the Foreign Intelligence Surveillance Court (FISC). Technology companies initially denied knowledge of the program but later acknowledged providing data in response to legal orders.
Tempora: GCHQ’s Tempora program, revealed by the Snowden documents, tapped into undersea fiber-optic cables at the points where they made landfall in the UK. By 2012, GCHQ was tapping over 200 cables simultaneously, giving it access to an enormous proportion of global internet traffic. The data was stored in buffers — internet content for three days and metadata for 30 days — and made available to NSA analysts.
XKeyscore: Described in NSA training materials as a system that covers “nearly everything a typical user does on the internet,” XKeyscore allowed analysts to search through vast databases of intercepted communications using selectors like email addresses, phone numbers, and keywords. The system was shared across Five Eyes partners.
Muscular: A joint NSA-GCHQ program that tapped into the private fiber-optic links connecting Google and Yahoo data centers around the world. Unlike PRISM, which operated under legal authority, Muscular appeared to operate by covertly accessing private network infrastructure, a distinction that drew particular criticism.
Bulk Metadata Collection: The NSA’s bulk collection of domestic telephone metadata — recording the number, time, duration, and location of virtually every phone call made in the United States — was confirmed by FISC court orders revealed by Snowden. This program, authorized under Section 215 of the Patriot Act, collected metadata from millions of Americans with no connection to terrorism.
European Parliament Investigation: The 2001 Temporary Committee on ECHELON confirmed the existence of a global interception system operated by Five Eyes nations and found evidence that it had been used for economic espionage against European companies, including in the Airbus-Boeing competition for a Saudi Arabian contract.
Debunking / Verification
This is a confirmed conspiracy. The Five Eyes alliance, its surveillance programs, and its global reach have been documented through classified materials, government admissions, and independent investigations.
Intelligence officials defend the alliance on several grounds: that it is essential for national security, that collection is targeted rather than indiscriminate, that oversight mechanisms exist through bodies like the FISC and parliamentary intelligence committees, and that the intelligence produced has prevented terrorist attacks and other threats.
However, these defenses have been substantially undermined by the evidence. The FISC was found to have operated as a rubber stamp, approving virtually every surveillance request presented to it. Congressional oversight committees were often uninformed or misled — Director of National Intelligence James Clapper famously told the Senate Intelligence Committee that the NSA was “not wittingly” collecting data on millions of Americans, a statement he later admitted was the “least untruthful” answer he could give.
The claim that surveillance is targeted rather than bulk was contradicted by multiple programs. The domestic metadata collection program swept up records of virtually all American phone calls. Tempora tapped cables carrying the communications of millions of people with no intelligence interest. XKeyscore’s capabilities for broad-based searching contradicted claims of targeted collection.
Post-Snowden reforms have introduced some additional oversight, including the USA Freedom Act of 2015 which ended the NSA’s bulk collection of domestic phone metadata. However, critics argue that fundamental surveillance capabilities remain intact and that the Five Eyes’ global architecture continues to enable mass collection of communications worldwide.
Cultural Impact
The Snowden revelations about Five Eyes surveillance triggered the most significant global debate about privacy and government power since the Church Committee hearings of the 1970s. The impact extended across technology, politics, law, and culture.
Technology Industry: The revelations fundamentally changed the relationship between Silicon Valley and the intelligence community. Technology companies, embarrassed by their apparent cooperation with surveillance programs, invested heavily in encryption and security measures. Apple introduced end-to-end encryption for iMessage, Google encrypted internal data center links (a direct response to the Muscular revelation), and the use of HTTPS encryption across the web accelerated dramatically. The “crypto wars” between governments seeking access and technology companies implementing encryption became a defining policy debate.
Legal and Policy Reform: The Snowden disclosures triggered reform efforts in multiple Five Eyes nations. The US passed the USA Freedom Act (2015), ending bulk domestic metadata collection. The UK passed the Investigatory Powers Act (2016), which for the first time placed some surveillance activities on a legal footing (though critics argued it also legalized practices previously conducted covertly). Courts in multiple countries ruled aspects of Five Eyes surveillance illegal.
International Relations: The revelations that the NSA had tapped the phones of allied leaders, including German Chancellor Angela Merkel, caused significant diplomatic damage. Brazil, Germany, and other nations brought proposals for internet governance reform to the United Nations. The revelations contributed to the European Court of Justice’s invalidation of the US-EU Safe Harbor data transfer agreement.
Public Consciousness: The phrase “Five Eyes” entered common usage. Surveys showed significant increases in public concern about government surveillance. The Snowden case generated Citizenfour (2014), an Academy Award-winning documentary, and the Oliver Stone film Snowden (2016). Edward Snowden became one of the most polarizing figures of the decade — variously characterized as a traitor and a patriot.
Journalism and Whistleblowing: The Snowden disclosures demonstrated the power of whistleblowing and investigative journalism to expose government overreach. Glenn Greenwald, Laura Poitras, and Barton Gellman’s work was recognized with Pulitzer Prizes and other awards. The case also highlighted the risks faced by whistleblowers and sources, influencing debates about press freedom and whistleblower protection.
Timeline
- 1941-1945 — US-UK intelligence cooperation during World War II; Bletchley Park codebreaking
- 1946 — UKUSA Agreement signed, formalizing US-UK signals intelligence sharing
- Late 1940s-1950s — Canada, Australia, and New Zealand added as full partners
- 1960s-1980s — Cold War expansion; global network of listening posts and satellite stations built
- 1988 — New Zealand journalist Nicky Hager first reports on ECHELON system
- 1999 — Australian journalist Duncan Campbell publishes detailed ECHELON exposé
- 2001 — European Parliament Temporary Committee confirms ECHELON’s existence and capabilities
- September 2001 — 9/11 attacks; massive expansion of Five Eyes surveillance under counterterrorism justification
- 2001-2007 — NSA bulk metadata collection, PRISM, and other programs established largely in secret
- June 2013 — Edward Snowden begins disclosing classified documents through Glenn Greenwald and Laura Poitras
- June 6, 2013 — PRISM program revealed by The Guardian and Washington Post
- June 21, 2013 — Tempora program revealed
- July 2013 — XKeyscore capabilities revealed
- October 2013 — NSA tapping of Angela Merkel’s phone revealed; diplomatic crisis
- 2014 — Citizenfour documentary released; wins Academy Award
- June 2015 — USA Freedom Act ends NSA bulk domestic metadata collection
- 2016 — UK passes Investigatory Powers Act regulating (and legalizing) some surveillance
- 2018 — Five Eyes issue joint statement demanding tech companies provide encryption backdoors
- 2020s — Five Eyes focus shifts to Chinese technology threats; alliance remains active
Sources & Further Reading
- Greenwald, Glenn. “No Place to Hide: Edward Snowden, the NSA, and the US Surveillance State.” Metropolitan Books, 2014.
- Harding, Luke. “The Snowden Files: The Inside Story of the World’s Most Wanted Man.” Vintage, 2014.
- Hager, Nicky. “Secret Power: New Zealand’s Role in the International Spy Network.” Craig Potton Publishing, 1996.
- Campbell, Duncan. “ECHELON: The World Under Surveillance.” Heise Online, 1999.
- European Parliament. “Report on the Existence of a Global System for the Interception of Private and Commercial Communications (ECHELON Interception System).” A5-0264/2001.
- Poitras, Laura (director). “Citizenfour.” 2014. Academy Award winner for Best Documentary Feature.
- Aid, Matthew M. “The Secret Sentry: The Untold History of the National Security Agency.” Bloomsbury Press, 2009.
- Bamford, James. “The Shadow Factory: The NSA from 9/11 to the Eavesdropping on America.” Anchor Books, 2008.
Frequently Asked Questions
What is the Five Eyes alliance?
Do Five Eyes nations spy on each other's citizens to circumvent domestic surveillance laws?
How did Snowden's revelations change understanding of Five Eyes?
Infographic
Share this visual summary. Right-click to save.